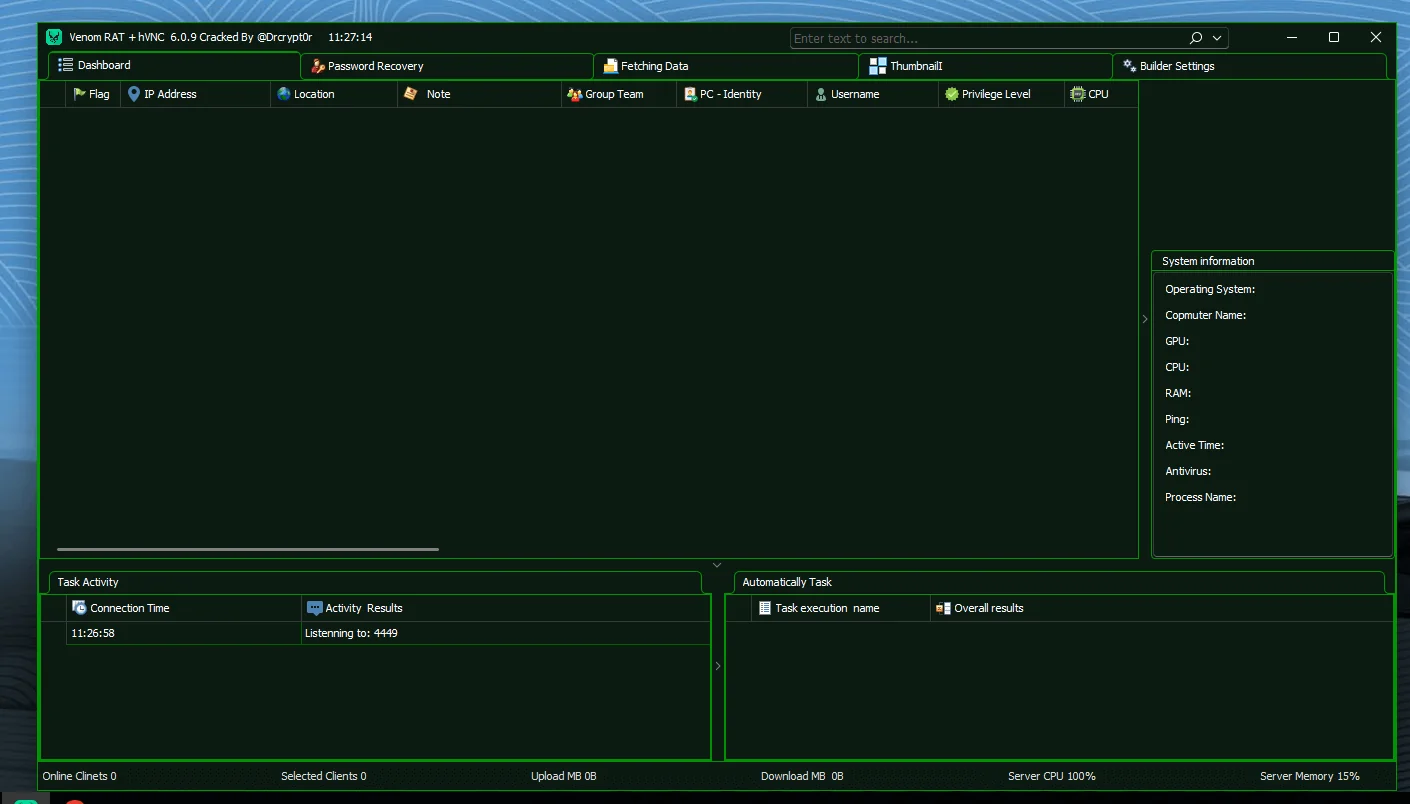
Venom Pro 6.0.9 RAT Cracked

Core Architecture of Venom RAT 6.0.9
Understanding the architecture helps cybersecurity professionals detect and mitigate threats effectively.
1. Command-and-Control (C2) Infrastructure
Venom RAT operates on a client-server model:
C2 Server (Attacker Panel): Control dashboard
Stub (Payload): Installed on victim machine
Reverse Connection: Victim connects outbound to attacker
This reverse communication allows it to bypass firewalls and NAT protections in many cases.
2. Builder Configuration & Payload Customization
The builder panel allows attackers to generate customized malware payloads.
Network Configuration Options
Custom server IP or DNS
Configurable listening port (commonly 4449)
Reverse TCP connection
Persistence Mechanisms
Startup registry modifications
Installation in %AppData%
Mutex to prevent duplicate instances
Anti-Analysis & Evasion Features
Venom RAT 6.0.9 includes multiple defensive bypass techniques:
Anti-VM detection (avoids virtual machines)
Windows Defender bypass
UAC privilege escalation
Process respawn (anti-kill protection)
Registry manipulation
Delayed execution (sleep timer)
These features make detection harder for traditional antivirus solutions.
hVNC: The Most Dangerous Feature
The inclusion of hVNC (Hidden Virtual Network Computing) makes this version especially threatening.
What Is hVNC?
Unlike traditional remote desktop tools, hVNC creates a hidden Windows desktop session invisible to the victim.
This means:
The victim cannot see mouse movement
No visible windows open
No indication of active control
The attacker operates in a completely hidden desktop environment.
Hidden Browser Exploitation
Within the hidden desktop, attackers can launch:
Chrome
Firefox
Edge
Brave
Internet Explorer
This allows criminals to:
Access banking portals
Log into email accounts
Bypass session-based authentication
Conduct financial fraud
Because actions occur within the victim’s actual system environment, security systems may interpret activity as legitimate user behavior.
Password Recovery & Data Theft Capabilities
One of the most powerful modules in Venom RAT 6.0.9 Cracked is its credential harvesting system.
Browser Credential Extraction
It supports a wide range of Chromium and Gecko-based browsers, including:
Google Chrome
Mozilla Firefox
Microsoft Edge
Opera
Brave
Vivaldi
Yandex
Comodo Dragon
Torch Browser
The malware extracts:
Saved passwords
Cookies
Autofill data
Browsing history
This enables account takeover without brute force attacks.
Application Credential Theft
Beyond browsers, Venom RAT targets:
Discord tokens
FileZilla FTP credentials
Email client logins (Outlook, Thunderbird)
Stored cryptocurrency wallet data
This creates a multi-layered compromise scenario affecting personal, financial, and corporate assets.
Surveillance & Monitoring Modules
Venom RAT 6.0.9 includes extensive spying capabilities.
Keylogging
Online and offline keylogging
Keystroke storage and later exfiltration
Password capture in real time
Webcam & Microphone Access
Live microphone listening
Audio recording
Webcam capture
This transforms infected systems into surveillance devices.
Desktop Monitoring
Screenshot capture
Remote file browsing
Hidden command-line execution
These features allow attackers to monitor victim activity continuously.
Fileless Execution & Advanced Attack Techniques
One advanced capability is memory-based payload execution.
Instead of writing malicious files to disk, Venom RAT can:
Download payloads directly into memory
Inject into legitimate processes
Export as shellcode
This helps evade:
Application whitelisting
Traditional antivirus scanning
Signature-based detection
Cryptocurrency Clipper Module
The clipper functionality monitors the clipboard for crypto wallet addresses such as:
Bitcoin
Ethereum
Litecoin
Bitcoin Cash
When detected, the malware replaces the copied address with the attacker’s wallet.
This type of attack can lead to irreversible financial loss.
Automation & Botnet Management
Venom RAT supports task automation:
Auto-password recovery on connection
Scheduled command execution
Remote updates
Bulk command deployment
This enables large-scale botnet management with minimal manual effort.
USB Spread & Lateral Movement
The malware can propagate through USB devices by:
Copying itself automatically
Hiding files
Creating autorun execution triggers
This method can bypass network segmentation and air-gapped environments.
Why Venom RAT 6.0.9 Cracked Is a Serious Cyber Threat
The combination of:
hVNC stealth access
Credential harvesting
Financial theft modules
Surveillance tools
Anti-detection mechanisms
makes Venom RAT a full-scale cyber weapon rather than a simple RAT.
The cracked version dramatically increases risk because:
It is freely distributed
No verification of buyers
Rapid global adoption
Frequent repackaging by other threat actors
How to Protect Against Venom RAT & Similar Malware
For general users:
Never download cracked software
Enable Windows Defender or reputable antivirus
Use two-factor authentication
Avoid opening unknown email attachments
Disable USB autorun
For IT administrators:
Monitor outbound traffic anomalies
Enable endpoint detection and response (EDR)
Restrict PowerShell usage
Enforce least privilege policies
Monitor registry startup keys
For cybersecurity professionals:
Develop behavioral detection rules
Monitor hidden desktop session creation
Track suspicious clipboard monitoring processes
Implement memory scanning tools
Venom Pro 6.0.9 Cracked
MediaFire is a simple to use free service that lets you put all your photos, documents, music, and video in a single place so you can access them anywhere and share them everywhere.
www.mediafire.com

